Opportunities
Doctoral Student Opportunities: The following research labs have funded openings for brilliant and highly motivated doctoral students.
Latest News
-

-
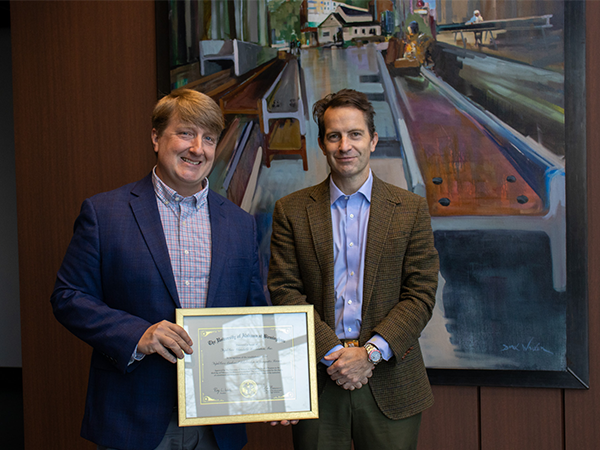 NaphCare Charitable Foundation invests in computer science at UAB“UAB continues to be an incubator for technological talent within Alabama. This scholarship underscores our dedication to expanding opportunities for future generations,” said Brad Cain, chief executive officer for the NaphCare Charitable Foundation.
NaphCare Charitable Foundation invests in computer science at UAB“UAB continues to be an incubator for technological talent within Alabama. This scholarship underscores our dedication to expanding opportunities for future generations,” said Brad Cain, chief executive officer for the NaphCare Charitable Foundation. -

